I thought it might be fun to make a follow-up to the Subpixel Snake video I did a few weeks ago. One regret I had after I posted my original video was that I didn’t show more of the game itself, and I only showed it on my iMac screen. So for this video I decided to show what it looks like on a variety of devices.
This was a ton of work, and I actually recorded more screens than what I showed in the video. However, most devices seem to use either an RGB stripe or BGR stripe subpixel geometry, and I was a little worried it could get boring if I showed a 20 screens and most of them were those 2, so I whittled things down to what I thought were the most interesting.
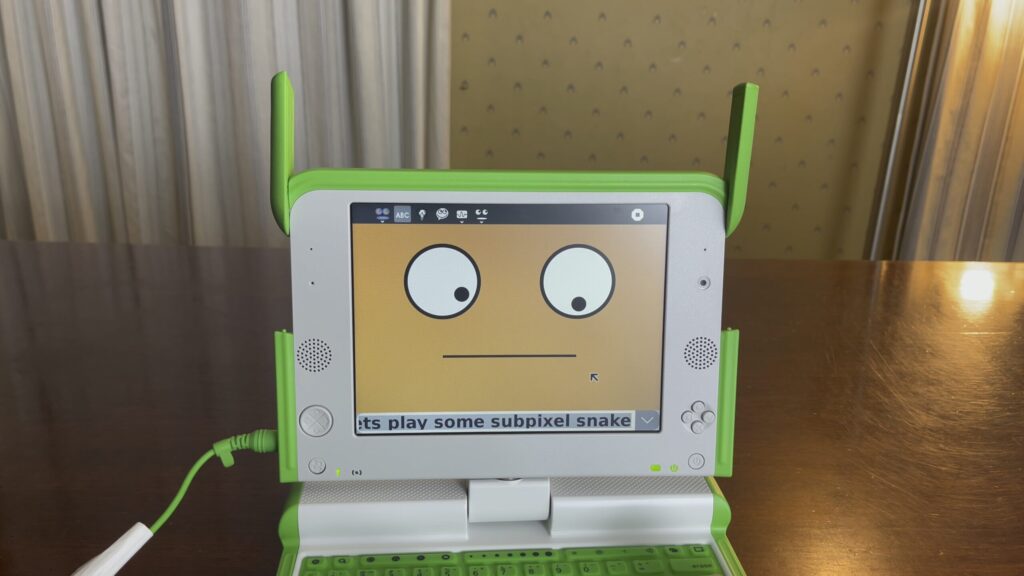
I really wanted something cool to end with (even though most people don’t make it to the end of a video), and I wound up hearing about this computer called the OLPC XO that had a unique subpixel layout. It’s screen had 2 modes: a monochrome mode for use in sunlight (similar to the Game Boy), and a backlit/color mode for use in darkness. When in color mode, each pixel would become either a red, green or blue subpixel along a diagonal line.
The thing even had a really cool story. It was supposed to be this $100 laptop that was going to change the world – children in developing countries would get access to a computer and the internet with one of these devices. They’d be able to learn about open source and linux and have access to the same information as we do in the developed world. There were even plans to add a hand crank as a way to give the machine power. Sadly though, the initiative failed, though they gave it a good shot and made a few hundred thousand of these devices.
Anyway, it just sounded really cool device and the perfect way to end the video, so I picked one up on eBay for $125. Initially was going to sell it afterwards, but it’s actually a lot of fun. The only downside is that it looks like you can only enter your name in once when setting up the computer, and because of the wonky keyboard I typed “Pzt” instead of “Pat” ????.
Anyway, if you have some time check out the video, and if you enjoy it please like / comment / share it!









 . As for the remaining 16 unlikes, I assume that most of those were people who just wanted to see the confetti animation again. These people were probably super confused by the message that popped up, and they probably thought I was some super sensitive prude or something. In hindsight, it does seem like an odd gag to put in a fine art photography website.
. As for the remaining 16 unlikes, I assume that most of those were people who just wanted to see the confetti animation again. These people were probably super confused by the message that popped up, and they probably thought I was some super sensitive prude or something. In hindsight, it does seem like an odd gag to put in a fine art photography website.