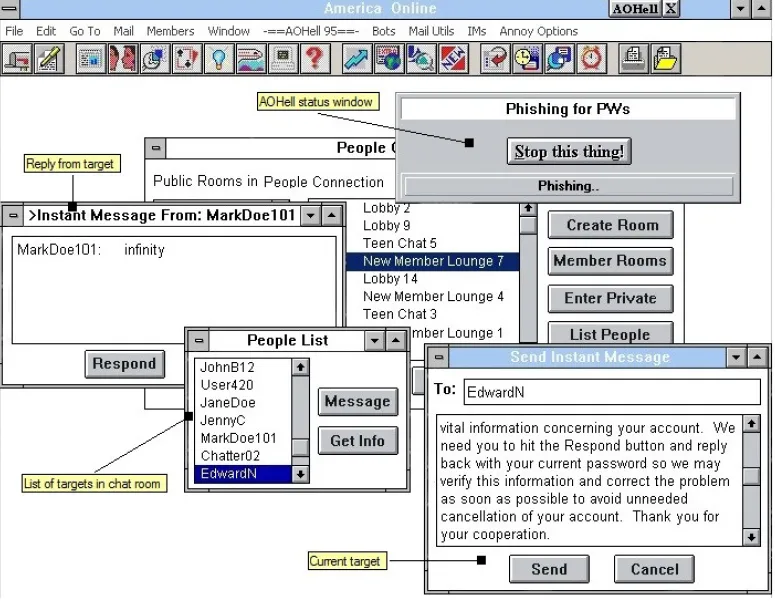
I’m getting ready to upgrade my computer, and while going through some old files I stumbled across Fate Zero, the last version released of infamous Fate-X application. The tool was popular way back in the late 90’s since it added a lot extra functionality to AOL – some of which AOL was ok with, and some of which it wasn’t very fond of. It was created by two mysterious individuals known as MaGuS and FunGii. After Da Chronic (known for AOHell), MaGuS was probably the most widely known AOL hacker. Even though Fate-X 2.5 and 3.0 had a much bigger impact, Fate Zero was the most extensive in regards to features.
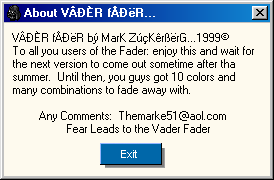
To maintain its status at the top of the heap, Fate Zero had to protect its external data, and this meant encrypting it so that other developers couldn’t snatch it up for their own progs. The prog scene of that time, however, is now long dead. Seeing these files today, I got curious. MaGuS was only 16 when he wrote Fate Zero. When I was 16, I knew almost nothing about encryption. It wasn’t until I was in college that I got a good exposure to the field of cryptography. Even though MaGuS seemed like a pretty smart guy, at that point in time he probably also didn’t know much about encryption. This made me think that the files might be easy to crack. It seemed like a fun way to spend a few hours, so I decided to see if I could decode them.
Interestingly (or not interestingly, depending on how you feel about it), the biggest source of external data for Fate Zero was AOL ASCII Art (ASCII Art done in 10pt Arial). This was typically used for scrolling into chat rooms. Fate Zero had over 500 files dedicated to this. You can see an example piece of art and its corresponding file encoding, below.
.--··´¯¯¯¨˜`·-.,
.---··· ´¨¨¨ `·.
.·´ ',
,' ',
¦ /| | / |
', ( \\:\ | /| /''\ .| |
'·. \|\ \.,'.|::\|\/ |¸,.-·´¨¨`·/.·´ | |
` ·-\\|'/|¨`, `|˜¨|¨˜`·„¸ | |´¯`, |
,'/||', \:'| , |_\::':/ | |, ,' |
,'//| ',¯¯·', | | ¯ |
,'/ | | ` ·. --·´ | | |
|´ | | _ ` ·.__ .·´ | |/_ |
| | |¨¯ ¯¯///,··\ ,.--·| | ',¯¨¨˜˜``'
|.·´| |--,··´¯//\ \ \ // Aeka _¸'·-By KioNe
File data for the above picture:
MDRæ”…f”…f”…f”…f”…f”…f¡’ý�)�õ��ý¦�¡“rn~�f”…f”…f”“sŽ¡�ý�”�î
�…f”…f”…f”…f”…f”…fÁ,“Sk�…f”…f,�f”…f”…f”…f”…f”…f”…f”…f”…f”…f”…moæ”…rˆ”…f”…f”…f”…f”…f”…f”…f”…f”…f”…f”…f”…fˆ rP�”…ì”…f”…f”…f£áf”…f”…”…f”…f”…f”…f”…f”…f”…Ân~�f”Œr”…fœ…f”…¢½®Áfð…f£áf”…f£Œm½”…f”“”…f”…f”áSk�…f”…m�¢…f½ðÁf½¢‘m🀽ðÁuð�r¡�ú
�Åý¢�ú”áf”…f”…f”áSk�…f”…f”Åf�¡Á¢Ý›”Â
Ô‘f”…fÁðýîÝ�ý¦�ø�f”…fð…fð�õÁ …f”áSk�…f”…f”…f›”ÂÝ›‘f½®ŒÂ …f”…ÂÀП€ˆ®”f”…fð…f”ár”‘m”…fðrP�”…f”…f Œuð…fˆ �õ�›‘f”…f”…f”…f”…f”…”…fÝ”�f”…f”…Ân~�f”…f”‘m”…”áfÁ”�t”’s�)…f”…f”…f”…fð…f”…”…f”…f”…Ân~�f”…f”áú”áf”áf”ÄfÁ”�tÀÓ…t�)…f”…f”áf”…f𔥔…f”…fÝoæ”…f”…”…”…Â
$…f�$”u �ý½”…f”‘tŽ¡�”…f”áf›‘õ
�ýÞÁÔŒSk�…f”…fð“ý�ð…fð’s,�ú�£”¢Ð…¢”…f£…fµÊ±Â”…¥�›�s£í…‘Ê㳫n~
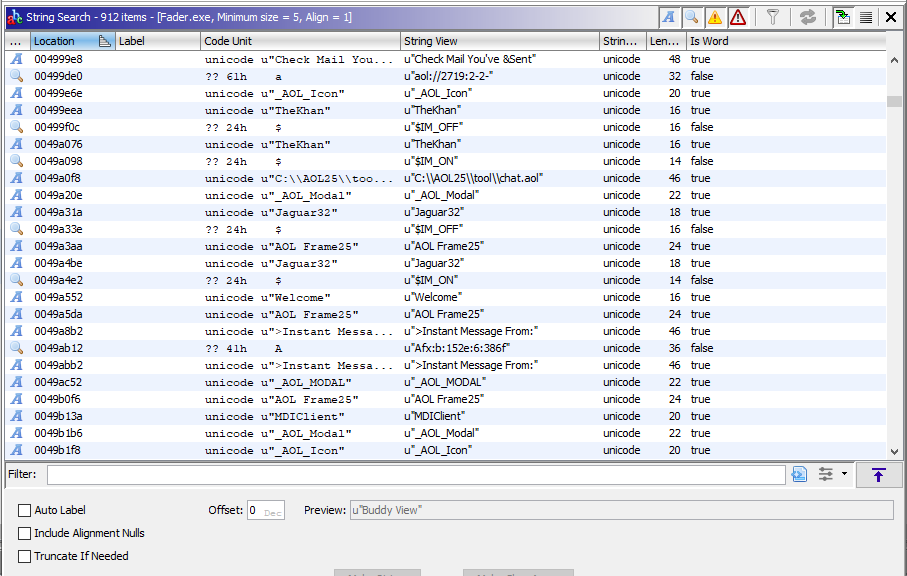
So right away it’s clear he’s not using a simple substitution cipher, yet due to the repeated use of white space in the source data, a pattern does seem to emerge in the encoded data. I compared the file sizes and found MaGuS’ encoded *.mdr files to be 5 bytes larger than their decoded counter parts. I chalked this up to the “MDR” that prefixed all the files, and the ending carriage return and line feed that seemed to end all of the files.
That meant there was probably one-for-one character encoding going on. After trying a few things out, I realized every 4th character seemed to use the same encoding. My guess was that he was combining 4 simple substitution ciphers, and using a different cipher depending on the index of the character. I created a quick script that read in an input/output combination and then tried to use that information to decode an encrypted file. To my delight, the script (mostly) worked! This was great, however, without knowing the full map of each cipher, I would only be able to get partial results.
I looked further and found each cipher was simply doing a character offset, meaning each cipher was a Caesar Cipher. The offsets were 70, 97, 116 and 101, respectively. If you look up the corresponding ASCII code for those numbers, you get the word “Fate”. I tried out this new decoding strategy and was able to successfully decode a directory of MaGuS’ files. I had broken the code! MaGuS was using what is known as the Vigenere Cipher, and for that particular directory, “Fate” was the pass-phrase.
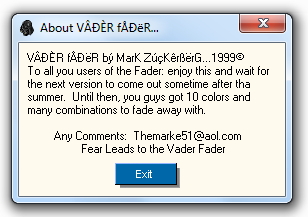
In another interesting twist, I noticed certain types of files used different Vigenere keywords. For his *.mdf data files, the keyword “12151981” was used. My guess was that this was his birthday, since this date would have made him 16 when the prog was released and he mentions that he was 16 in the app’s about section. In this same about section he also mentions that he’s Asian and what high school he went to. This narrows down who he is to almost a T.
This got me thinking: “I wonder if I can track down who MaGuS was?” With the aid of some crafty googling, email addresses taken from webpages mentioned inside of Fate (if you dig through the machine code, you’ll find a dozen or so URLs), Rapportive (which can be used to look up social profiles based on email addresses), the internet archive, and leads taken from Fate Zero itself, I was able to pin point an individual who fit all of the criteria and was friends with people who got shout outs in Fate. I plugged their name and the “12-15-1981” birthday into dobsearch.com, and only one result came back, and it was from the state and city MaGuS said he lived in. I was stunned, I had found MaGuS.
I feel like it’d be wrong to out him, but at the same time I know it’d be a cop-out to not say anything. So I’ll just say that according to his LinkedIn and Facebook, he works for a consulting firm in the Washington DC area and is specializing in web related work. The rumors of him working for a security firm or of being this guy are false. He also seems to be somewhat of world traveler, and has a side hobby of being a photographer.
Part of me wondered for a second if I should contact him. He was a big inspiration to me back in the day, and Fate-X and its ilk are what led me to learn how to program. However, after talking with my wife, we thought that’d be too creepy. He made some cool progs a long, long time ago, no need to freak him out with some elaborate story that involves breaking some encryption he wrote over a decade ago.
Anyway, after I’d finished my little side quest, and I realized I still had 500+ decrypted AOL ASCII Art files, many of which haven’t seen the light of day in over a decade. Since some of that stuff is kind of cool, I decided to create a gallery for it. If you have a few moments check it out. Also, feel feel to grab and host any art there that you like, just be sure to leave in any artist signatures. It’s kind of strange to think that era is so far away, but also kind of neat to find remnants of it every so often.
2013.04.28 Update: A bit more has happened since I made the original post. MaGuS actually emailed me to congratulate me on the finding and to confirm his identity (though I’ll continue to respect his anonymity). He also mentioned that at the time he wrote Fate he had no training or knowledge of programming, and that he came up with his own encryption method as he went along. I don’t fault him for this, as Fate is still really impressive and I think most of us were in the same boat back then. He seems like a pretty cool guy, and I was glad to hear he enjoyed the post.
2016.03.10 Update: To reconnect with fellow former AOL developers: